Digital Twins and Cybersecurity: Making the Most of Their Power
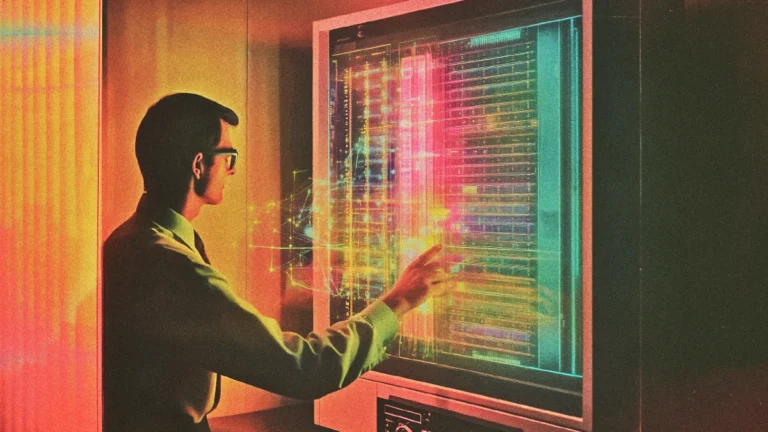
As cyber threats become more sophisticated, traditional defenses struggle to keep up. A robust technological ally in this battle is the Digital Twin, a virtual representation of physical systems that mirrors and simulates real-world operations in real-time.
This tech marvel provides an unprecedented opportunity to secure critical systems, detect vulnerabilities, and predict attacks.
This article explores how digital twins can revolutionize cybersecurity and what challenges must be addressed to unlock their full potential.
What is digital twin technology?
A digital twin is a virtual replica of a physical object, person, or process that can be used to simulate its behavior to better understand how it works in real life. Digital twins are linked to real data sources from the environment, which means that the twin updates in real time to reflect the original version.
The twins also comprise a layer of behavioral insights and visualizations derived from data. When multiple digital twins are interconnected within a single system, they create what is referred to as an enterprise metaverse.
This digital and often immersive environment replicates and links every facet of an organization. This enables the optimization of simulations, scenario planning, and decision-making processes.
Role of digital twins in a cybersecurity plan
Digital twins can create virtual replicas of an organization’s IT infrastructure, including its networks, systems, and devices. By simulating various cyberattack scenarios without impacting the real-world environment, the cybersecurity team can identify potential vulnerabilities and weaknesses.
This allows for proactive risk assessment and mitigation to enhance cyber resilience.
They can also:
- Identify exposures and breaches in real-time
- Fortify incident response planning
- Security testing and validation
- Create network twins
A network of digital twins cuts through these challenges by providing a comprehensive, real-time replica of the network, enabling seamless validation and verification of configurations and security policies across individual network components.
Subscribe to our bi-weekly newsletter
Get the latest trends, insights, and strategies delivered straight to your inbox.
Risk and challenges of incorporating digital twin solutions
Below, we will examine some of the risks and challenges that can jeopardize the integrity and operation of digital twins in a business environment.
Secured and protected digital twins
It is importantto secure the digital twin itself to prevent malicious actors from using it as a proxy to attack the physical system. If attackers gain access to a digital twin, they can potentially use it as a ‘blueprint’ for real-world attacks – further leading to security breaches, sabotage, or even physical harm.
Hence, encryption, robust authentication, and continuous monitoring of digital twin system are essential to mitigate these risks.
Data integrity and privacy concerns
Digital twins rely on massive amounts of data from physical systems, so data integrity and privacy become imperative. Any unauthorized modifications or data theft could compromise the twin’s exactness and, by extension, the security of the physical system. Moreover, ensuring that data is up-to-date and accurate is vital for maintaining the effectiveness of cybersecurity defenses.
Therefore, organizations must adopt robust data protection protocols and ensure transparency in terms of data collection, usage, and storage policies. This will help maintain trust and reassure individuals and stakeholders about the safety of their information.
Cost and complexity
Deploying and maintaining a digital twin system requires significant investment in human resources and financial capital. Startups or small organizations may struggle with the high costs of implementing this technology.
Moreover, they need to ensure the team has enough skilled staff to handle this new technology. Hence, proper budgeting and planning are required to move ahead with this new technology.
Ownership issues
The creation of a digital twin involves various components—software, algorithms, data, and the physical entity itself. Determining who owns the digital twin system can be challenging, especially when multiple stakeholders are involved.
Clarifying rights and ownership early in the development process is crucial to avoid disputes and ensure that all parties benefit fairly from the technology
Future of digital twin tech in cybersecurity
The future of digital twins in cybersecurity is promising, with numerous advancements and improvements on the horizon.
As this technology continues to evolve, its integration with AI, Blockchain, and 5G will play a critical role in shaping the future of cybersecurity, enabling organizations to stay ahead of increasingly sophisticated cyber threats.
- Integration of AI in digital twin for automation and efficiency
AI can enable adaptive security systems, which can automatically adjust security settings based on real-time data from digital twins. These systems can detect emerging threats and rapidly reconfigure defenses to mitigate risks.
Additionally, AI can enhance predictive maintenance by continually learning from digital twin data and by refining its ability to predict and prevent cyberattacks.
- Blockchain for digital twin security
Blockchain’s inherently secure, transparent, and immutable nature makes it an ideal tool for safeguarding digital twins. By encrypting and tracking all data exchanges within the digital twin, blockchain can significantly reduce the risk of data tampering or unauthorized access.
It is especially useful for supply chains and industries that rely heavily on secure data transmissions.
- 5G’s connectivity for efficient data transfer
The widespread deployment of 5G networks will revolutionize the potential of digital twin technology in cybersecurity. With its fast speed, minimal latency, and comprehensive coverage, 5G will make data movement between digital and physical twins easier.
This faster connection will enhance real-time synchronizations, remote control, and procedure and asset tracking.
In brief
Digital twins are not just digital environments but the future foundation of a more secure, adaptable, and intelligent cybersecurity landscape. They represent a groundbreaking approach to cybersecurity.
The possibilities are exciting, but they also remind us of the need to stay ahead of emerging threats.